Update 01/01/21: As kindly pointed out by Zagzigger in the comments section below, ESNI is not working for many users on the newer versions of Firefox. The issue unfortunately seems unlikely to be fixed, as ESNI is an outgoing technology that will be eventually be replaced by the more comprehensive ECH. Details on ECH: https://blog.cloudflare.com/encrypted-client-hello/ The ECH technology stack is on track to be added to Firefox in 2021.
What’s SNI?
SNI stands for Server Name Indication. It’s an extension to TLS that allows multiple online services (websites) with unique encryption certificates to share the same IP address.
Wait…what’s TLS? And “encryption certificates”?
TLS, or Transport Layer Security, is a protocol used to encrypt (or scramble) data passing over the Internet so that it cannot be intercepted on the way. Let’s say you’re doing a bank transaction online. You will not want a “middle man”, say your internet provider, your Wi-Fi network admin, or a nefarious hacker, to snoop on the transaction. This is where TLS comes in handy. It is part of a software stack that allows online services to protect sensitive data transfers by encrypting them on the way to your computer or mobile device.
Any website aiming to provide an encrypted connection requires a digitally signed certificate assigned to it. Such certificates can be obtained from an authorized vendor such as Comodo, Let’s Encrypt, Cloudflare, VeriSign, etc.
Why encrypted SNI?
There’s been a recent trend to encrypt all communication that happens online, be it the content of websites or DNS queries to access those sites. Part of this is a push to improve privacy of all types of data transfers (not just sensitive data), and part is due to broad availability of encryption options at zero to little cost. Encrypted sites also fare better on Google search results, which is a nice little incentive on top.
SNI is a weak link in this equation as it’s not encrypted by default. An SNI request includes the website address in plain text, allowing your internet provider to detect and block that request. Encrypted SNI was introduced as a proposal to close this loophole.
Read more about encrypted SNI and Firefox’s support on Cloudflare…
Note that the proposal is still under review, has undergone multiple revisions, and may take years to become a standard. Encrypted SNI also works only when it’s been enabled on both client (your computer) and server (the website) side. All this is to say that the support in Firefox is currently experimental and will continue to improve as the draft for eSNI matures.
How to enable eSNI in Firefox?
Firefox is currently the only web browser to support eSNI. Other browsers are expected to follow suit when the proposal becomes a standard.
Before enabling eSNI, I will recommend enabling encrypted DNS in Firefox. Unencrypted (or “plain text”) DNS defeats the purpose of eSNI, so follow these quick steps to encrypt it first:
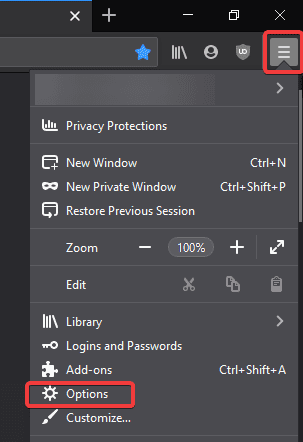
Open Firefox, and go to Tools (⚙) > Options.
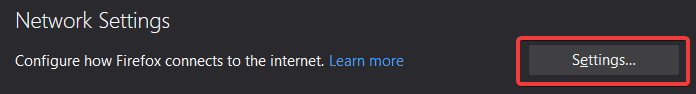
Scroll all the way down to Network Settings and click the Settings… button.
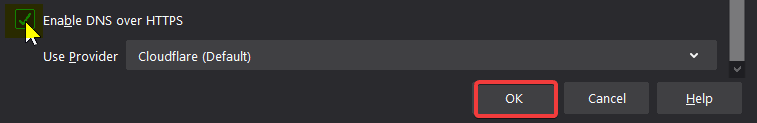
Once again, scroll all the way down to “Enable DNS over HTTPS”. Select your DNS provider, enable the option, and click OK.
Now that DNS over HTTPS (DoH) is on, follow these steps to enable eSNI:
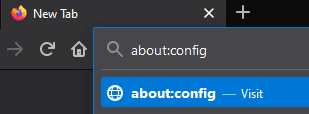
In the Firefox address bar, type about:config and hit Enter.
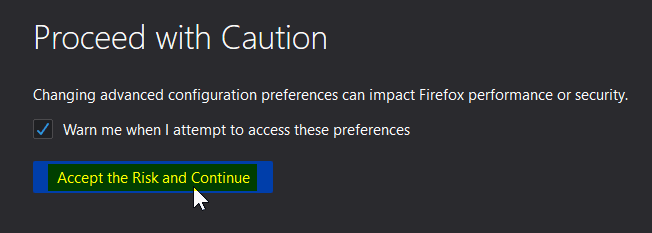
Accept the prompt to “proceed with caution”.
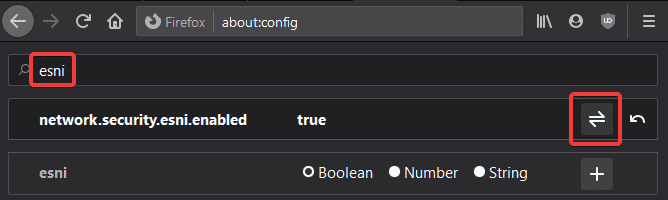
Search for “esni” and click the “Toggle” button next to network.security.esni.enabled to enable this switch.
That does the job. Firefox will encrypt SNI requests to websites that support the feature, and your browsing sessions will be a bit more private.




Doesn’t work with 86.01
That’s correct. You will need to use Firefox Extended Support Release for ESNI. It’s currently on version 78.9. Hopefully, ECH will be standardized and implemented soon.
For more on this go here: https://bugzilla.mozilla.org/show_bug.cgi?id=1667801
I don’t like to be too harsh, but this to me is very disappointing by Mozilla.
It seems to be yet another case where technical decisions have been made and implemented without regard to the overall picture. Very poor, and unfortunately common.
Thanks for the link! I had no idea this is such a mess of a situation. ESNI continues to work for me on two Windows laptops and one Ubuntu VM, but I suppose that’s not gonna last for long.
https://i.imgur.com/nfibKkc.png
https://i.imgur.com/ayPT2yT.png
I completely agree with you on this decision made by Mozilla. I still love Firefox but it gets a little harder to do so sometimes! Here’s hoping everyone gets on the same level wrt ECH implementation.
Thanks again, and my wishes for a great year ahead!
Hi,
I’m on 84.0.1 on FreeBSD, and followed the instructions – and double-checked.
It has worked in the past – but this time, it shows ESNI as not working.
Any thoughts?
Hi,
Could you expand on this a bit? Do you see ESNI as off when visiting this page – https://www.cloudflare.com/ssl/encrypted-sni/
If yes, you can double check if DoH and ESNI are configured correctly in about:config. Set “network.trr.mode” to 3 to enable strict DoH.
Yes, checked as suggested.
network.trr was set to 2 – but changed it to 3 – made no difference
Everything else as instructed (but network.security.esni.enabled is Boolean not String)
This definitely worked on previous versions of Firefox – unless it is something to do with underlying FreeBSD software.
Thanks for your help.
You could stay on the Firefox Extended Support Release channel if it’s available for FreeBSD. Mozilla doesn’t mention BSD support on their page but it seems official packages are available as mentioned here. I should clarify that I’ve no experience with FreeBSD. I did fire up a Linux VM to check ESNI and it worked as expected. Thanks for stopping by.
Not working too on firefox for windows.
Unfortunately as pointed out by Zagzigger, there seems to be an issue between Firefox’s implementation and the latest draft proposal for ECH. ESNI is on track to be replaced by a more comprehensive solution called ECH, and from the looks of it Firefox is pulling the plugs on ESNI before ECH is anywhere near to completion. https://bugzilla.mozilla.org/show_bug.cgi?id=1667801
Funny thing is ESNI continues to work for me on FF 84.0.1 two laptops running Windows and an Ubuntu VirtualBox VM. I’ve no idea why that’s case, but I suppose it will likely stop working for me soon.
https://i.imgur.com/nfibKkc.png
https://i.imgur.com/ayPT2yT.png